如要在 Firebase 控制台中快速測試更新後的 Firebase Security Rules,請使用規則遊樂場。
探索新行為時,或是在編寫規則時快速驗證規則,都可以使用規則遊樂場這項便利工具。系統會顯示訊息,確認是否根據您為模擬設定的參數允許或拒絕存取。
使用規則測試區
- 開啟 Firebase 控制台,然後選取專案。
- 接著,從產品導覽中執行下列其中一項操作:
- 視需要選取 Realtime Database、Cloud Firestore 或「儲存空間」,然後按一下「規則」,前往編輯器 Security Rules。
- 完成編輯後,按一下編輯器中的「規則遊樂場」。
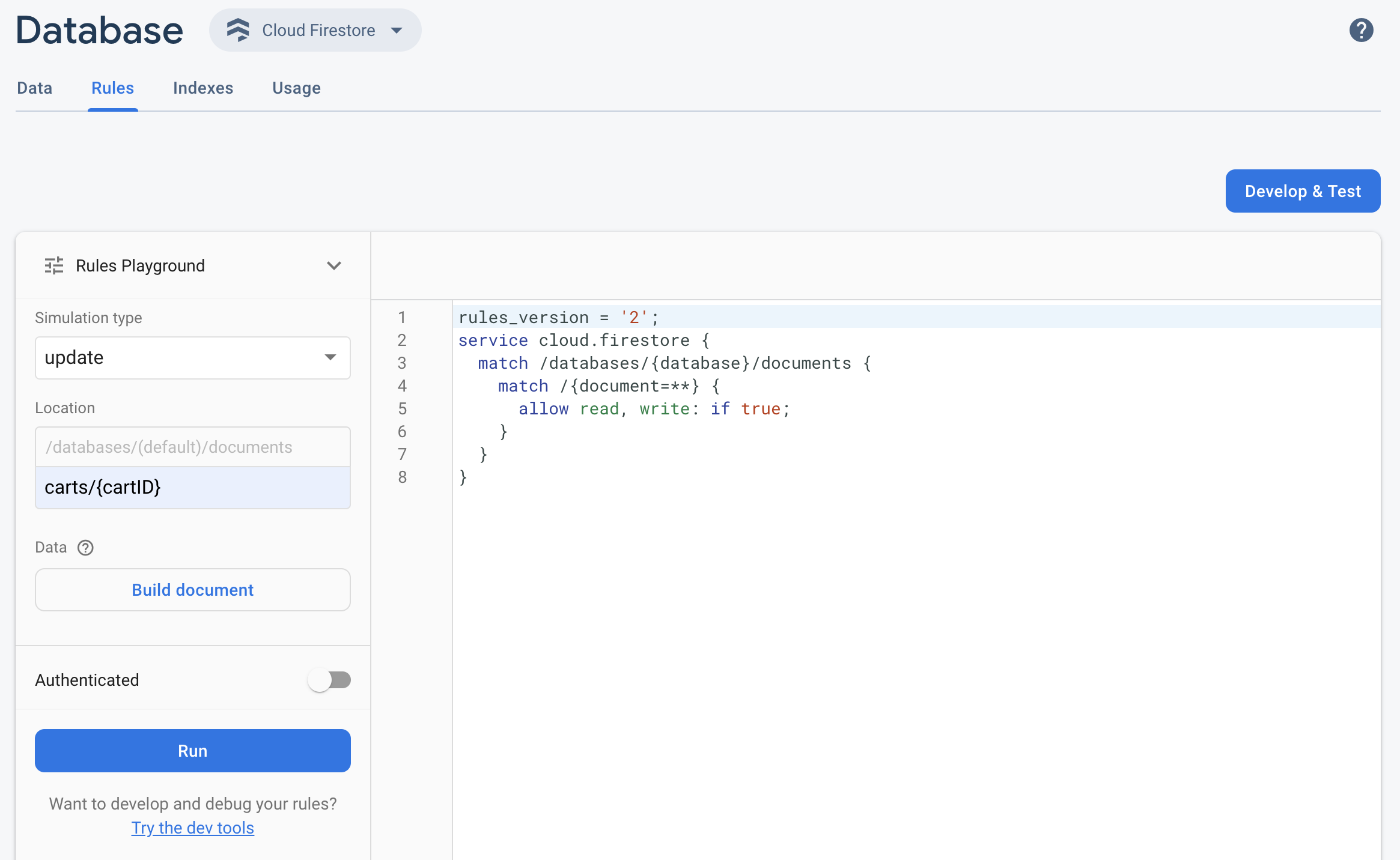
- 在「規則遊樂場」設定中,選取測試選項,包括:
- 測試讀取或寫入作業。
- 資料庫或儲存空間 bucket 中的特定「Location」(位置),以路徑形式表示。
- 驗證類型:未通過驗證、已通過驗證的匿名使用者,或特定使用者 ID。
- 規則明確參照的文件特定資料 (例如,規則要求必須有特定欄位,才能允許寫入)。
- 按一下「執行」,並在編輯器上方的橫幅中查看結果。
規則模擬工具情境範例
請使用下列範例情境和基本規則,測試規則 Playground 的行為。
Cloud Firestore
service cloud.firestore {
match /databases/{database}/documents {
// Allow only authenticated content owners access
match /some_collection/{document} {
allow read, write: if request.auth != null && request.auth.uid == request.resource.data.author_uid
}
}
}
Realtime Database
// These rules grant access to a node matching the authenticated // user's ID from the Firebase auth token { "rules": { "users": { "$uid": { ".read": "$uid === auth.uid", ".write": "$uid === auth.uid" } } } }
Cloud Storage
// Grants a user access to a node matching their user ID
service firebase.storage {
match /b/{bucket}/o {
// Files look like: "user/<UID>/file.txt"
match /user/{userId}/{fileName} {
allow read, write: if request.auth != null && request.auth.uid == userId;
}
}
}
在 Security Rules 編輯器中,新增提供的規則。
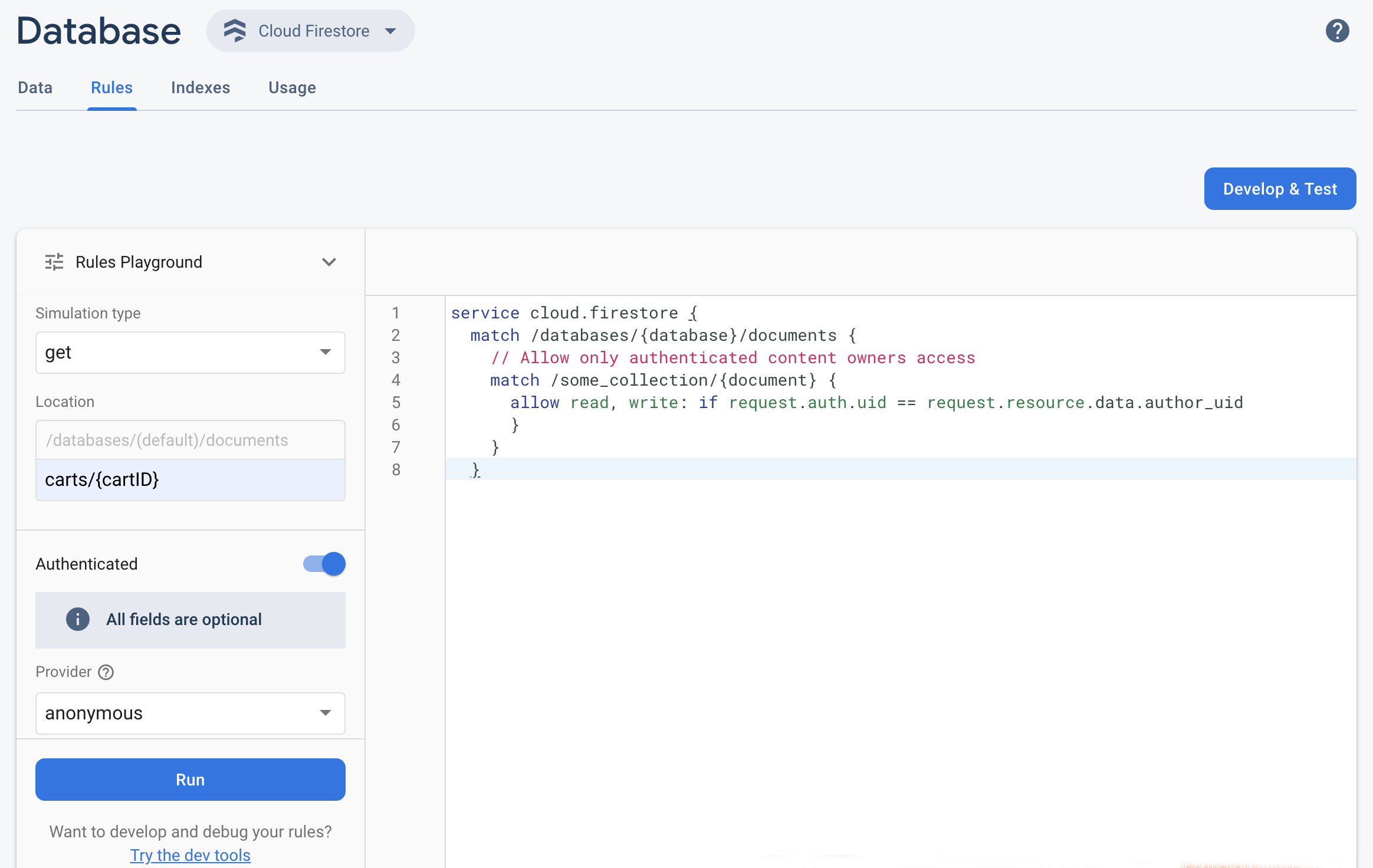 從「模擬類型」下拉式選單中選取「get」,並在「位置」欄位中輸入有效路徑。
從「模擬類型」下拉式選單中選取「get」,並在「位置」欄位中輸入有效路徑。開啟「驗證」,然後從「供應商」下拉式選單中選取驗證類型。
輸入使用者 ID 詳細資料,然後按一下「執行」。
模擬結果會顯示在編輯器頂端。根據您輸入的使用者 ID 詳細資料,系統會顯示橫幅,確認讀取要求已獲准或遭拒。

